SSL revisited (part 1 - CAA)
January 03, 2018A little while ago I wrote about improvements in the SSL configuration of my webserver. You can read about that here.
I decided to check my SSL configuration with Qualys’ SSL Server Test again to see if there was room for improvement. Sure enough, there was.
The report
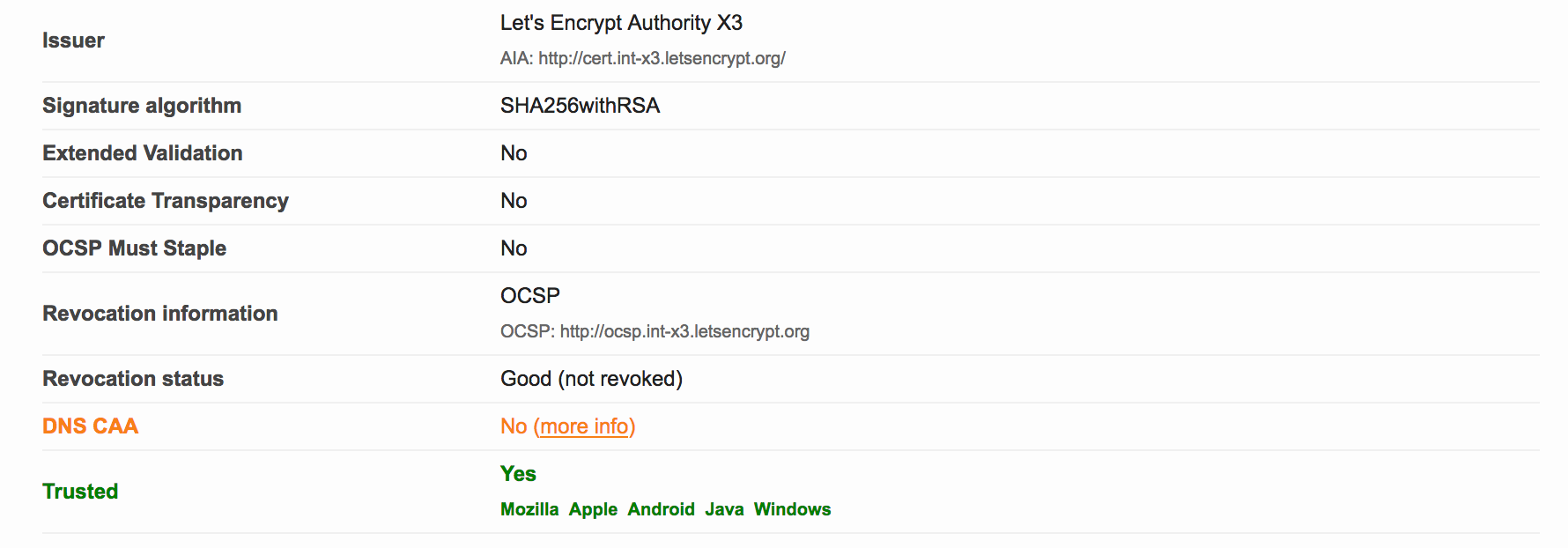
The report was still A+. However, I noticed two items that could possibly improved upon:
- No DNS CAA - I’ll address that in this post
- Weak 3DES ciphers - I’ll write another post about this
The cause
I had not yet implemented Certification Authority Authorization (or CAA), since I didn’t know what it was. The link in the SSL Labs report provides more information. In short, the PKI ecosystem is provided with a new control mechanism to restrict which CA’s may issue certificates for a specific domain. All you need to do is list the CA’s that you use for a specific domain in new CAA DNS record for that domain.
As of September 8, 2017, upon issuance of a new certificate for a domain, the CA is supposed to check the CAA records for that domain. If there is no matching CAA policy for the CA, the issuance should be denied (and it MAY be reported if the domain holder has iodef CAA record(s)).
From the RFC:
If the domain name holder specifies one or more iodef properties, a
certificate issuer MAY report invalid certificate requests to that
address. In the following example, the domain name holder specifies
that reports may be made by means of email with the IODEF data as an
attachment, a Web service [RFC6546], or both:
$ORIGIN example.com
. CAA 0 issue "ca.example.net"
. CAA 0 iodef "mailto:security@example.com"
. CAA 0 iodef "http://iodef.example.com/"
For those of you who want to have more in-depth information, see RFC 6844.
The solution
In my case, for voipmeister.com, I am using Let’s Encrypt as the CA for my certificates. So, if I want to implement a CAA policy, all I need to do is add DNS records like this:
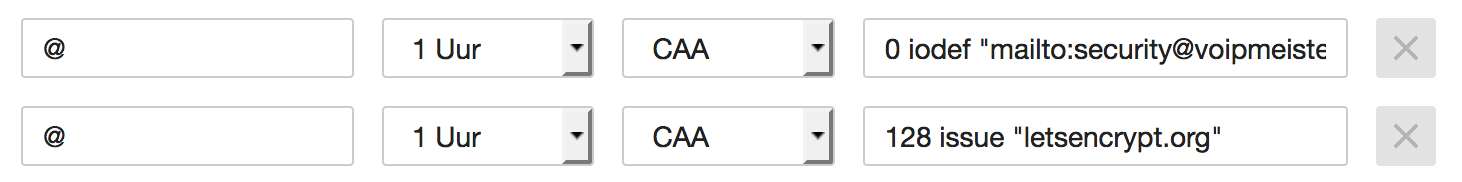
The second one tells any interested party that I only use Let’s Encrypt as my CA. The first record is a request to inform me at a specific email address upon violations or problems concerning certificate issuance. I created those DNS records by hand, but you may also use the SSLMate CAA Record Helper.
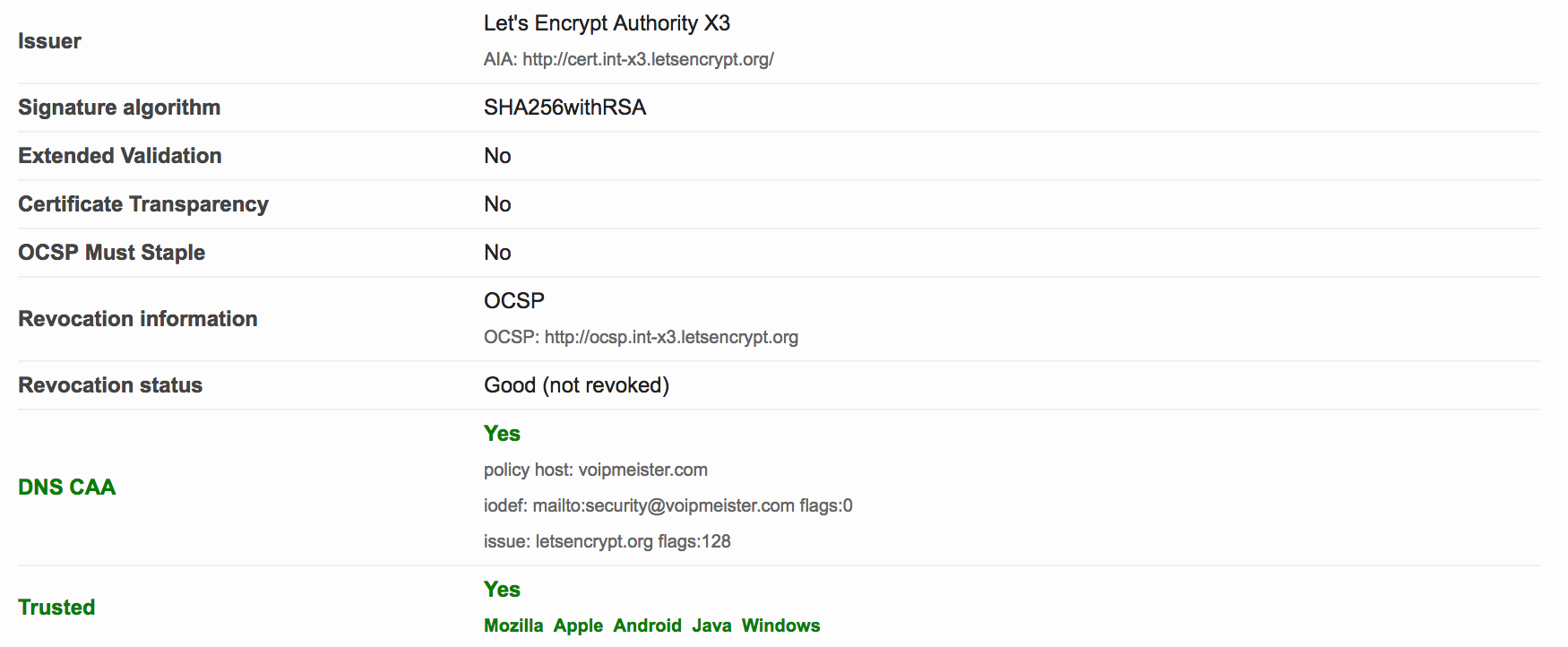
After we wait a while for the recent DNS change to take effect, we can recheck with the SSL Labs Tester. The result is this:
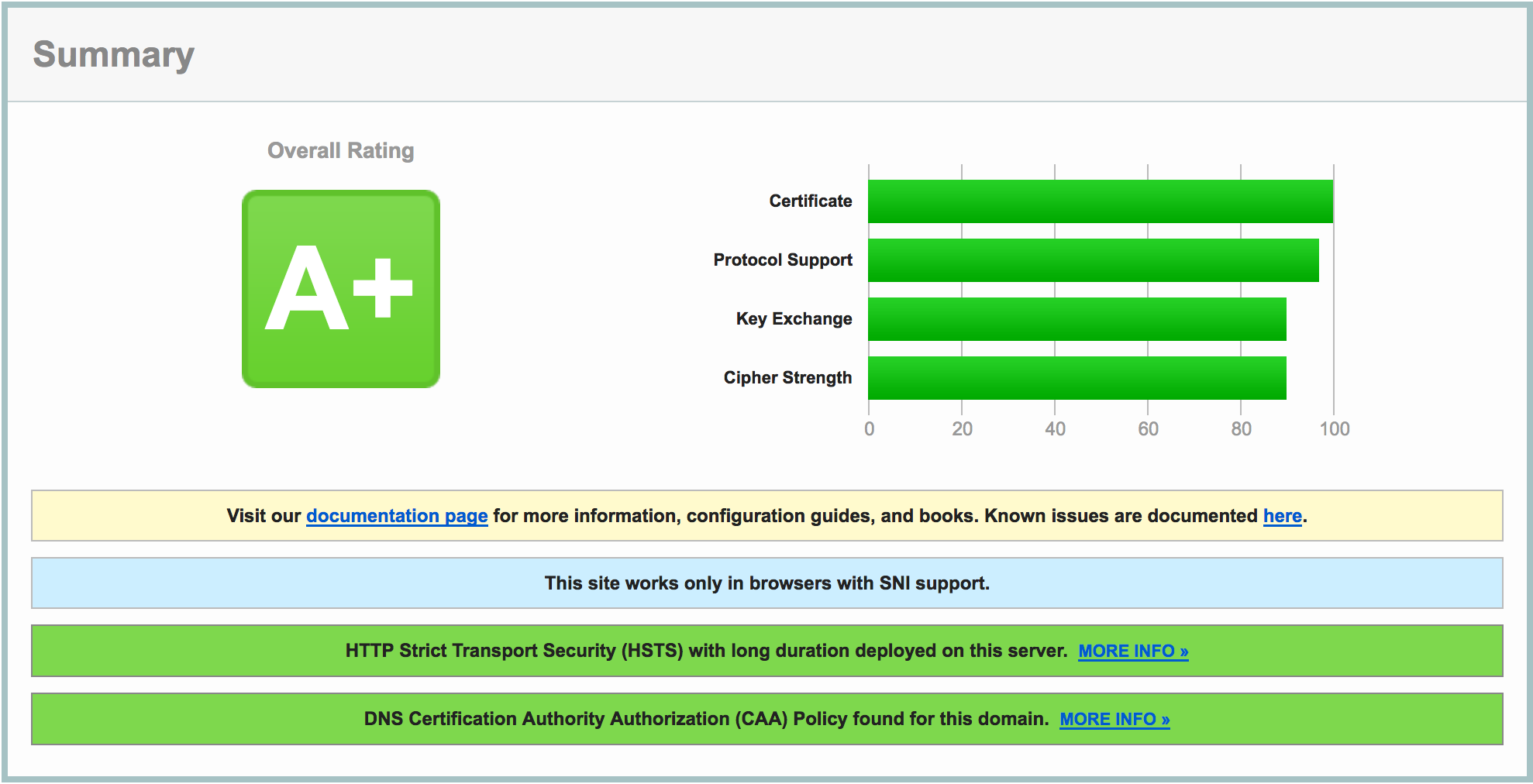
Do notice the extra green bar pertaining to CAA, and see the DNS CAA information in the details: